
SHA-256 Hashing: A Secure Algorithm for Data Integrity
Written by: Rugved Koshiya | 14 JULY

Written by: Rugved Koshiya | 14 JULY
Have you ever wondered how websites store passwords securely?
Or how you can verify the integrity of a downloaded file?
Or how cryptocurrencies like Bitcoin work?
If you have, then you might have heard of a term called SHA-256 Hashing a secure algorithm.
SHA-256 Hashing a secure algorithm is a process of transforming any given data into another value that is shorter, fixed-length, and unique. Hashing is widely used for encryption, authentication, digital signatures, and other applications that require verifying the identity or integrity of data.
In this blog post, we will explain what SHA-256 Hashing a secure algorithm is, how it works, and how to calculate one of the most popular and secure hashing algorithms: SHA-256. SHA-256 stands for Secure Hash Algorithm 256-bit and it can generate a 256-bit (32-byte) hash value for any data, whether it is text, image, video, audio, or anything else.
Hashing is a mathematical function that takes any input data and produces an output value called a hash or a digest. The hash value has the following properties:
Hashing is different from encryption in that encryption is reversible (you can decrypt the encrypted data with the right key) and encryption usually produces an output value that is similar in size to the input data.
Hashing works by applying a series of mathematical operations to the input data. These operations are designed to be fast, deterministic, and unpredictable. There are many different hashing algorithms, each with its own set of operations and rules.
One of the most widely used hashing algorithms is SHA-256. SHA-256 belongs to a family of hashing algorithms called SHA-2, which was developed by the US National Security Agency (NSA) in 2001. SHA-256 is considered to be very secure and resistant to attacks.
To calculate the SHA-256 Hashing a secure algorithm value for any data, we need to follow these steps:

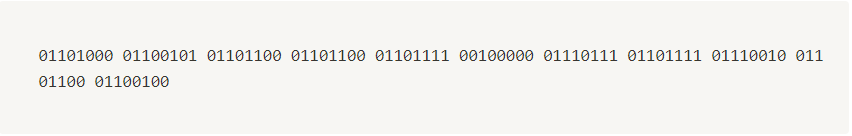
hello world then we get binary value from it.| Character | Decimal | Binary |
|---|---|---|
| h | 104 | 01101000 |
| e | 101 | 01100101 |
| l | 108 | 01101100 |
| l | 108 | 01101100 |
| o | 111 | 01101111 |
| (space) | 32 | 00100000 |
| w | 119 | 01110111 |
| o | 111 | 01101111 |
| r | 114 | 01110010 |
| l | 108 | 01101100 |
| d | 100 | 01100100 |
88 bits512 bits. At this step we reserve 64 bits from 512 bits for future use.
A chunk is a fragment of information.
Lets suppose we are having 2MB of data so we can divide it into 4 part of 512 KB so each 512 KB block called chunk.
1 and append all 0 until it’s length reaches to 488.
448 bits so now to make it 512 bits we add 64 bits to it. Now question is what we will add for 64 bits?88 bits whose binary representation is 01011000. so we add this as 64bit binary.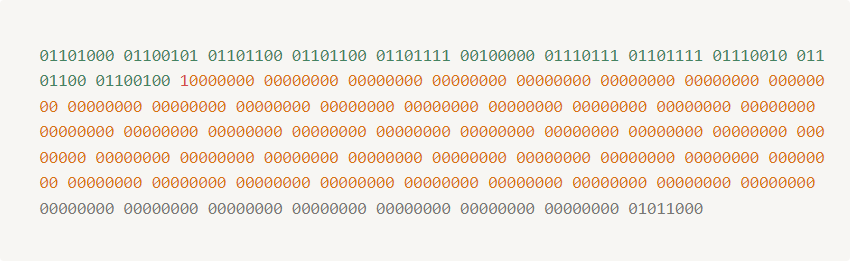
8 default hash value we call them name with h0, h1, h2, h3, h4, h5, h6, h7.square root of prime numbers and assign its fractional part to h0 → h7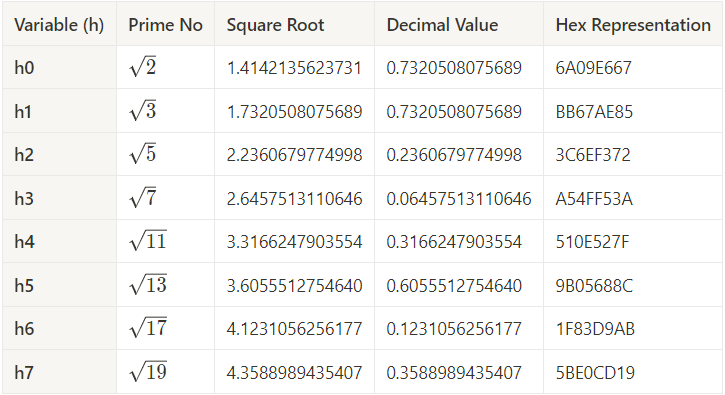
64 constant we call them name with k.2, 3, 5, 7, 11, 13, 17, 19, 23, 29, 31, 37, 41, 43, 47, 53, 59, 61, 67, 71, 73, 79, 83, 89, 97, 101, 103, 107, 109, 113, 127, 131, 137, 139, 149, 151, 157, 163, 167, 173, 179, 181, 191, 193, 197, 199, 211, 223, 227, 229, 233, 239, 241, 251, 257, 263, 269, 271, 277, 281, 283, 293, 307, 311cube root of prime numbers and assign its fractional part to k0 → k63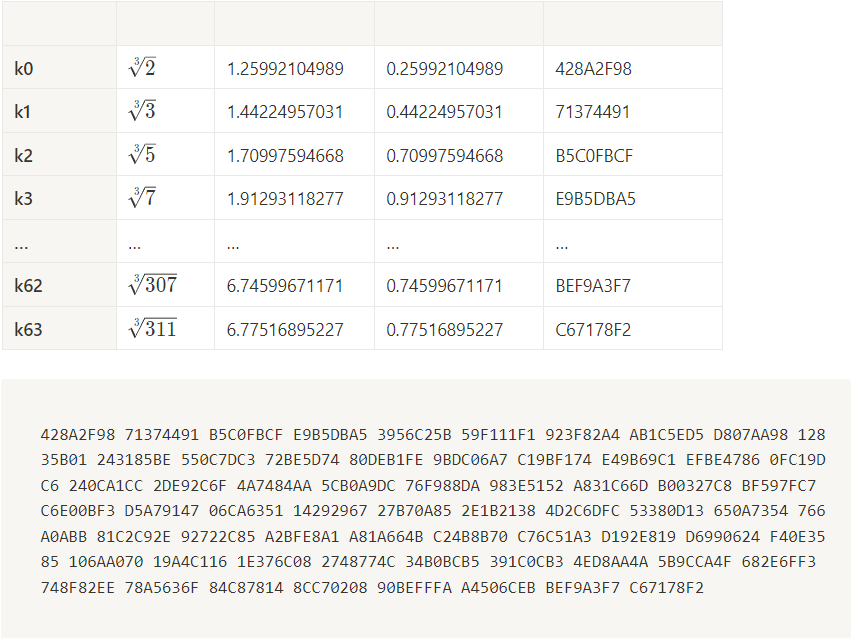
512-bit chunk of data from our input. In our case, because hello world is so short, we only have one chunk. At each iteration of the loop, we will be mutating the hash values h0 - h7 which will be the final output.8 bit binary format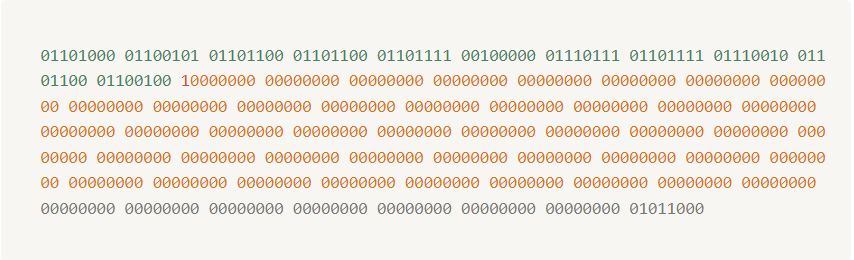
32 bit binary so it will look something like below: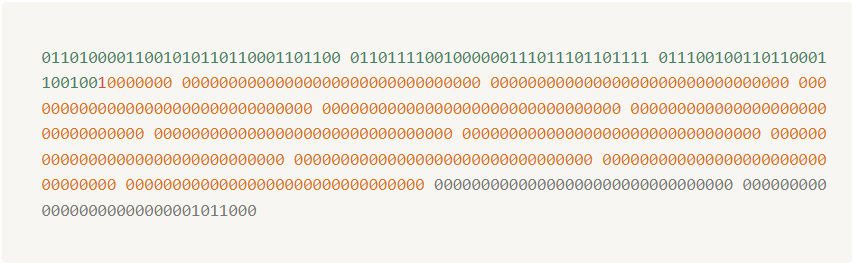
16 bits of 32bits so for completing 64 bits block we required $64 \space bits – 16 \space bits = 48 \space bits$0 in 32 bit representation in order to complete 64 bits.
Now we apply one formula and modify this appended 0 to increase complexity and it make sure that the hash value is not dependent on any single bit. If one bits gets change all hash value changes.
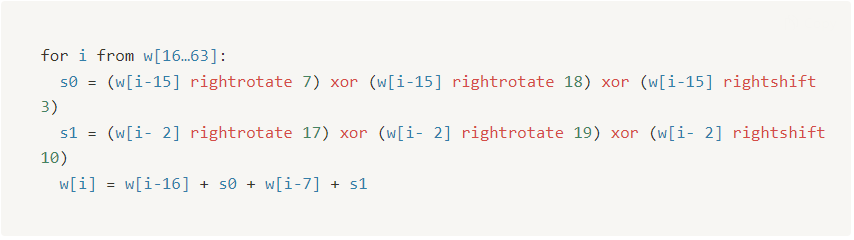
w[16] so we can see how it works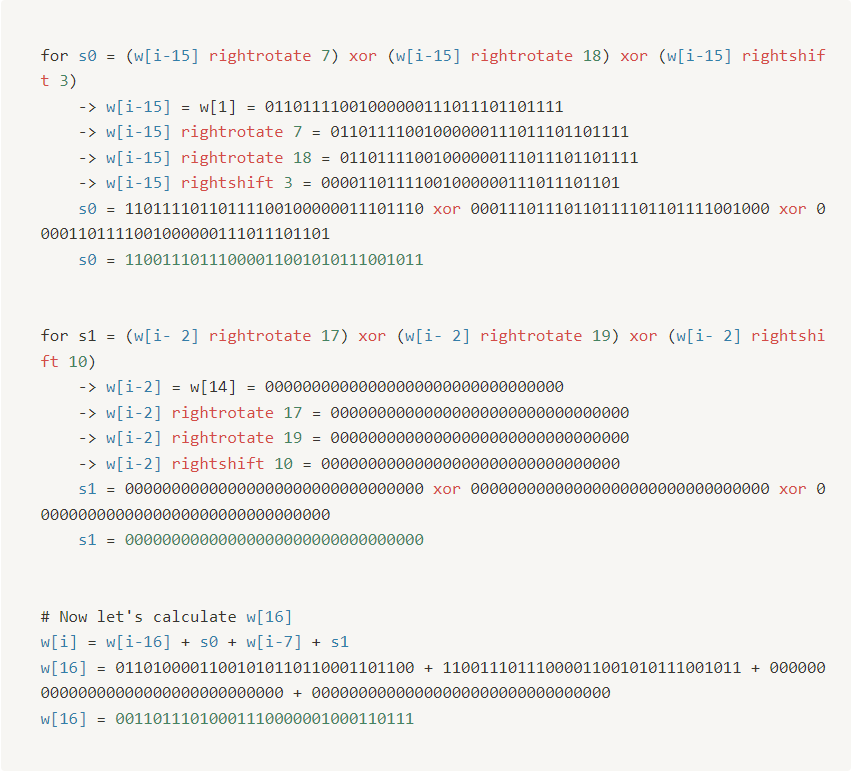
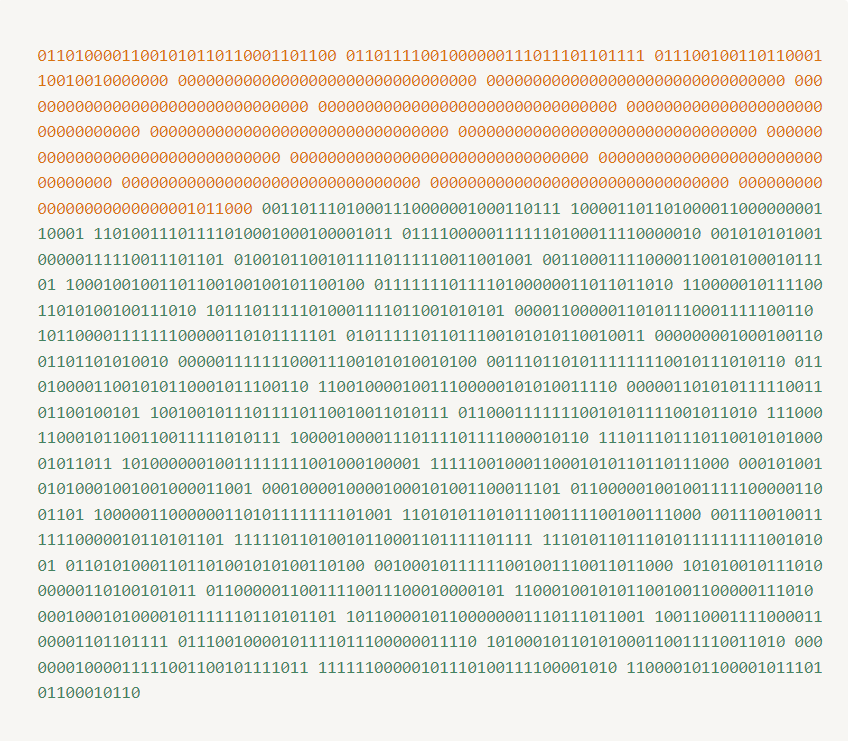
64 bit message scheduling block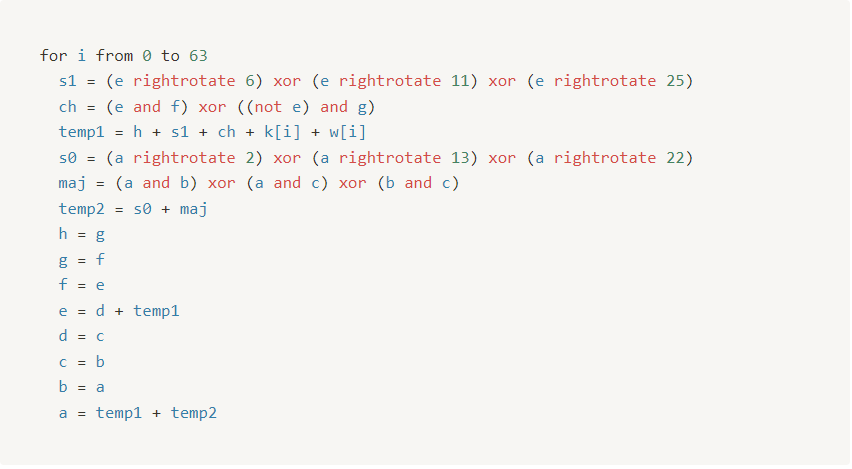
64 times we get value of a → h is given below :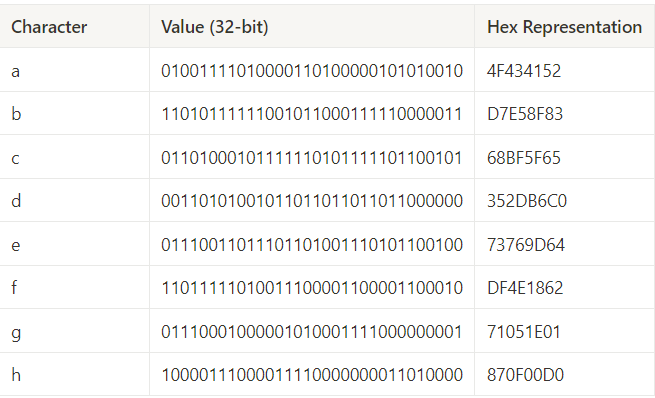
h0 → h7 is given below:
h0 → h7 values.
h0 → h7 and then repeat for next chunk with new updated h0 → h7 values.Hash value = h0 append h1 append h2 append h3 append h4 append h5 append h6 append h7
Hash value = B94D27B9 append 934D3E08 append A52E52D7 append DA7DABFA append C484EFE3 append 7A5380EE append 9088F7AC append E2EFCDE9
Hash value = B94D27B9934D3E08A52E52D7DA7DABFAC484EFE37A5380EE9088F7ACE2EFCDE9
B94D27B9934D3E08A52E52D7DA7DABFAC484EFE37A5380EE9088F7ACE2EFCDE9